Sports as the “battering ram”
In the News Corp Annual General Meeting in 1996, Rupert Murdoch reportedly said:
“Sport absolutely overpowers film and everything else in the entertainment genre… we plan to use sports as a ‘battering ram’ and a lead offering in all our pay television operations.”
Broadcasting of live sports has always been a major driver, if not the outright lead offer, for traditional pay-TV subscriptions. With recent advances in live streaming technology and new viewing options provided by vMVPD (virtual multichannel video programming distributors) implementing subscription-based or free ad-supported services, avid fans have been migrating from traditional broadcast to online services in droves, looking for lower-cost alternatives to high-priced pay-TV services. This trend is especially true for millennials, who appreciate the convenience of being able to watch their favorite content anytime and anywhere. Sports as the “battering ram” has not gone away, but instead has translated to OTT live streaming services and serious competition for traditional sports broadcasters.
The scourge of live sports piracy
Regrettably, not all online video services originate from legitimate sources let alone rights holders. The rapid growth and value of live streaming services has attracted the attention of professional pirates and multi-national crime syndicates. Illegitimate live OTT sports services have proliferated in many regions reflecting the global demand for streaming services, which has accelerated partly as a result of the pandemic lockdowns combined with the ease of access to such content on all kinds of consumer devices. This is causing significant economic harm to both subscription and advertising revenue. Sports rights holders are losing an estimated USD 28 billion a year per a study from Ampere Analysis in early 2021. The same report also estimates that 51% of sports fans use pirate services to watch live sports on a monthly basis, and that OTT sports streaming services would gain USD 5.4 billion by eradicating this piracy.
The changing face of live sports piracy
Modern content security technology that includes an anti-piracy strategy is essential for protecting the revenue of a premium live sports broadcast or streaming service. But protecting live sporting events with legacy conditional access systems (CAS) or even modern digital rights management (DRM) technology alone may not be sufficient to block piracy services. Today’s reality is that pirates effectively bypass CAS/DRM systems by restreaming live sporting content using various circumventing tactics such as screen recording software, external camera recording, or HDMI capture devices with a high-bandwidth digital content protection (HDCP) “stripper”.
While piracy of live sports is nothing new, what has changed is the content distribution technology. With traditional broadcast TV, piracy was initially focused on smart card cloning, or even full set top-box replication, followed by so-called control word sharing (rapid sharing of the content encryption keys over broadband), and later on stealing content using HDMI “strippers” between the set-top box (STB) and TV set.
With streaming it is different: the very technologies that have enabled live streaming in UHD/4K picture quality to large-screen TVs are now used to intercept and redistribute live sporting content to illicit subscribers. This trend marks a shift from traditional peer-to-peer (“BitTorrenting”) networks and illegal downloads towards real-time service theft and instant restreaming. In addition, there is a proliferation of Kodi-based STBs, in and of themselves not illegal since Kodi is a free and open-source media player application. Unfortunately, unscrupulous third-parties advertise “fully loaded” Kodi-boxes, which have been pre-loaded with software for accessing illegal streaming services. Virtual Private Networks (VPN) is another method often used to circumvent regional broadcasting restrictions, labeled geo-location fraud, and there are even VPN providers who advertise such capability to consumers.
However, piracy is shifting from the traditional focus on STBs and TVs to attacks on content delivery networks (CDN) in various forms. Pirates are able to mimic legit devices and systems using API endpoints and thus steal the content before it is even distributed. The CDN provider Akamai regularly issues its State of the Internet reports, and security and piracy figure increasingly in those reports.
To learn more about piracy in general, please read our blog post The forms of video piracy: there’s a taxonomy for that.
What is forensic video watermarking?
Forensic video watermarking (a.k.a. forensic watermarking or video watermarking) is a technology that is complementary to DRM and CAS, and it is a crucial element of an anti-piracy strategy. Forensic watermarking is used to imperceptibly alter video content (modification of a few pixels) to hide a unique identifier (forensic evidence, or “payload”). It is a similar concept to invisible ink and paper watermarks. In the case of OTT streaming, a multi-DRM service provides content protection for transport and storage, together with a license policy to define how the content may be consumed. Session-based and user-specific video watermarking enables the service operator to embed a unique identifier for each user. The ID is then used to trace any unauthorized redistribution of premium content. This technique is a critical anti-piracy tool to protect UHD premium content and live events broadcasting since it is possible to identify the actual device that is “leaking” or restreaming the content. This anti-piracy strategy allows for real-time detection of the source of pirated content and real-time shutdown of the illegal redistribution, and the ability to take other actions subject to the service provider’s policy.
Video watermarking techniques
Forensic watermarking can be applied either server-side, or in the client device itself. Any good anti-piracy strategy must also consider the type of content that is to be watermarked. For example, for live streaming services, minimizing latency is essential. Therefore, several issues must be considered when adding a forensic watermark. Server-side technology requires tight integration with the live encoder and edge components such as CDNs. It is computationally intensive, and may add latency to live event transmissions. Another approach is to focus on client-side watermarking technology to battle theft of high-value sports content. This approach leverages a thin client with pre-integration in the video player for different types of streaming devices. Fortunately, in many cases the client-side watermarking approach does not require the significant watermarking integration nor add the system overhead that is currently required for the server-side solutions. Moreover, in order to protect the thin watermarking client, white-box cryptography technology is used to protect the app code and associated secrets, and to securely anchor the client software to the device.
The importance of rapid video watermark extraction
Another key requirement for implementing an effective anti-piracy strategy to protect live sports content is the ability to perform a fast extraction of the embedded forensic watermark. Contrary to protecting a video download or VOD-streamed content with forensic watermarking technology that was optimized for a non-real-time model, we now face live event instant restreaming piracy, meaning a real-time solution is required. With server-side video watermarking technologies, the traditional approach by studios for protecting on-demand content, it could take several minutes to detect the watermark identifier once the pirated content has been identified and captured. This is far too long to effectively protect the revenue of a live event. Additional time is also required to identify the piracy and redistribution links and for responding to the piracy, which can include shutting down the source once the watermarking ID is extracted. An anti-piracy strategy for live sporting events requires forensic watermarking detection to be a near real-time process. Recent advancements in both server-side and client-side video watermarking solutions, especially for live streaming services, are aimed at better protecting the revenue of live sports.
Combining video watermarking with web monitoring tools
The first step in combating live sports piracy is to be able to detect the pirated service. It is essential that an anti-piracy strategy also takes advantage of web monitoring services and web crawling tools, in conjunction with forensic watermarking. Combining digital fingerprinting technology, which is required for automatic content recognition (ACR) applications, with session based forensic watermarking, will achieve the most effective end-to-end anti-piracy service. This combined approach enables web monitoring of known piracy sites for pirated streams and ultimately the detection forensics required to prosecute pirates and take action to disrupt the entire value chain from illicit source to consumer.
We’re here to help
Intertrust Expressplay offers video watermarking and anti-piracy services for media and entertainment as a fundamental part of the ExpressPlay Media Security Suite. ExpressPlay Anti-Piracy and Watermarking, powered by Friend MTS, offers an optimized Advanced Subscriber ID (ASiD) service for live streaming. This client-composited solution combines high-performance video watermarking and digital fingerprinting with automated content monitoring and legal enforcement. It is the most widely used watermarking solution globally, especially to protect live sports – it quickly identifies and disables illicit restreamers.
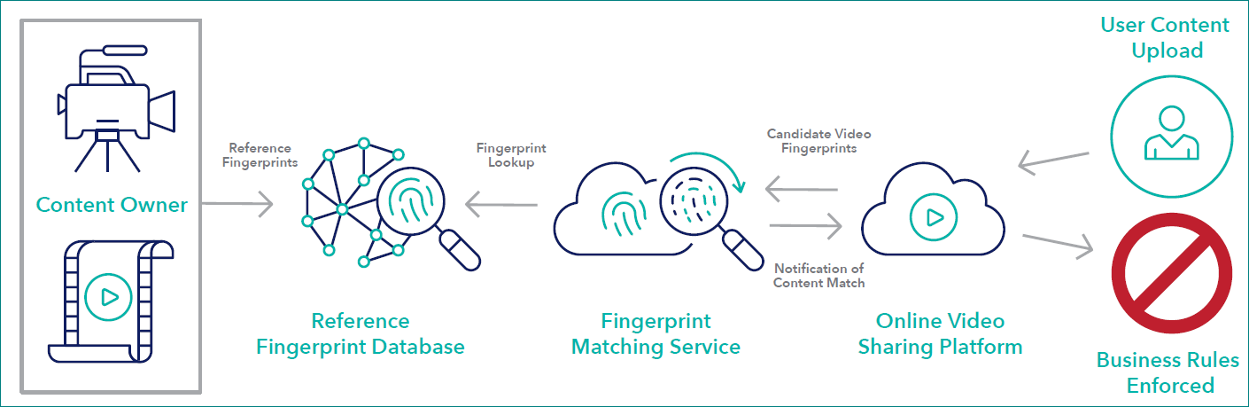
The Content Identification Service depicted in the diagram above, powered by Friend MTS, is the right approach for identifying pirated media. It relies on web crawling tools together with digital fingerprinting technology, enabling automatic content recognition to identify licensed content distributed by an unlicensed source. The service’s fingerprinting technology analyzes video content to produce a unique digital signature, or fingerprint. These fingerprints are transmitted in real time and stored in a vast index. As new video is monitored, it is compared against the index and the appropriate actions are immediately assigned.
ExpressPlay Watermarking enables a holistic live and on-demand content protection that allows watermarking-related applications to be managed together with cloud-based ExpressPlay multi-DRM service. To learn more, download our anti-piracy services datasheet, or talk to a friendly security specialist – no strings attached!