Liberate your data from constraints.
Your data’s effectiveness is held back by many factors. Where and how can you use it? How well does it operate with other data, if at all? Is it protected and can you safely share it with others?
Until now, to protect data, you’ve had to isolate it, restrict it, and hold it close.
The Intertrust Platform™ liberates you from these constraints.
Today’s key data challenges
Organizational risk
Data-driven organizations face legal risk, reputational risk, and operational risk, especially when sensitive data is present.
Data mismanagement
Organizations starting a digital transformation journey or looking to optimize their data workflows often have to overcome data management problems.
Business isolation
Growing a business cannot be an island. It must work with partners, vendors, and solution providers to explore new revenue streams through digital business models.
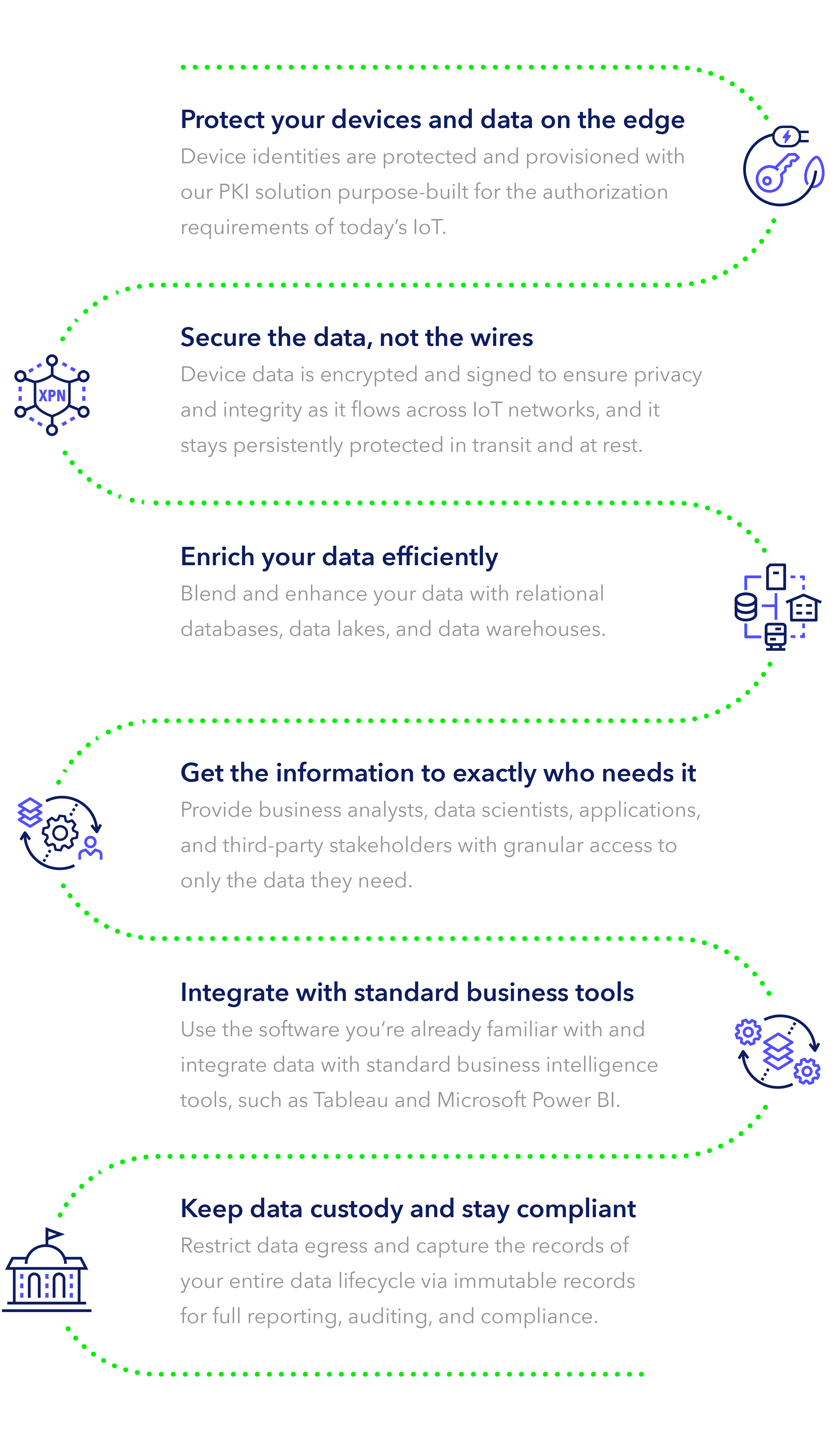
Unite device and data operations
Our suite of services let you manage data, devices, applications, and operations without constraints.
Share trusted data within your organization, with partners, and third-parties to take advantage of quicker, more meaningful insights to improve your business operations and foster new business opportunities.
Stay in control
Govern data flows by setting granular policies and audit trails to minimize your risks and liabilities.
Private and trusted
Gain end-user trust by persistently protecting data from edge-to-cloud, even across untrusted networks.
Don’t be locked in
Unite disparate platforms into a single virtual layer of distributed multi-party data. Secure your devices with vendor-agnostic device authentication.