Automotive
Delivering trust for the connected car, including trusted identities, secure device communication and authentication, and data integrity.

Delivering trust for the connected car, including trusted identities, secure device communication and authentication, and data integrity.
Learn about trusted ecosystems and mutual authentication, how device identities function, and provisioning device identities within complex IoT environments throughout their lifecycle.
The ecosystem that supports today’s connected car is an ever-expanding network of interconnected services and devices. But as it expands, it becomes more susceptible to threats that put data and sensitive information at risk. Trusted and authenticated identities are essential within this broad ecosystem.
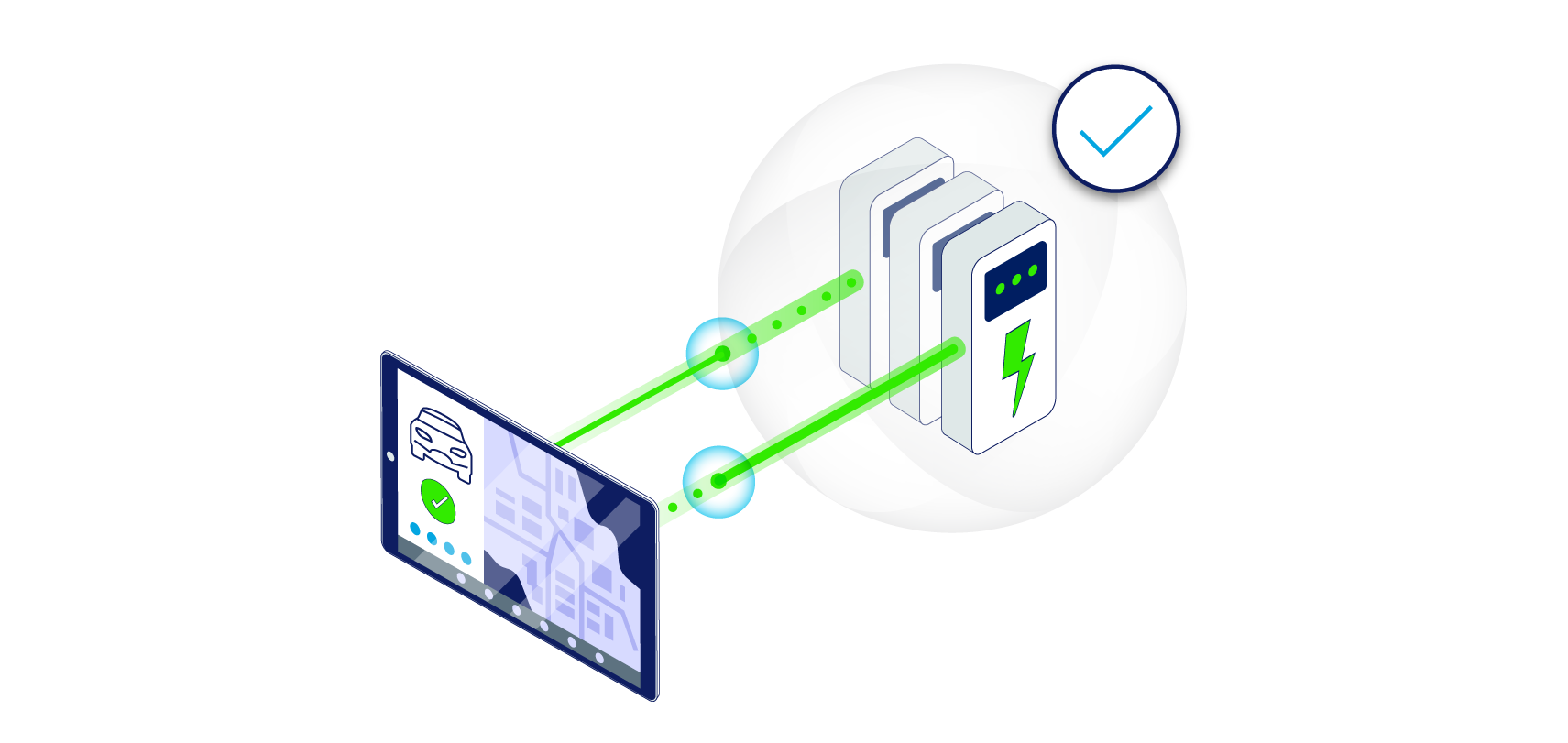
Intertrust enables trusted data exchanges between a multitude of devices, data and systems. The distributed trust it provides ensures that devices can gain access to data or services they need.
Facilitate governed data exchanges between partners, vendors, and service providers—with trusted, granular data sharing to specific datasets and applications.
Build a network of connected devices with trusted device identities. Through secure data interoperability, maintain data privacy, authenticity, and integrity.
Gain strong encryption, strong authentication, secure identities, and robust key management.
Gain real-time, interoperable IoT data intelligence and time-series data aggregation, to maintain and preserve ecosystem health.
Simplify, streamline, and automate digital certificates to authenticate the identity of devices at scale.
Automotive
One of the world’s largest automakers chose Intertrust to create a trusted data exchange ecosystem for managing its data access and application workflows. The Platform doubles as a secure environment that enables collaboration with third-party firms needing to use the automaker’s internal data to develop applications.